|
Abstract.
This article describes the use of Methodology for Critical
Infrastructure Identification-MI2C to identify the critical
part of telecommunication infrastructure in the scope of the XV Pan
American and Parapan American Game held in Rio de Janeiro in July and
August 2007.
1
Introduction
This article is organized as follows: section 2
presents the Methodology for Critical Infrastructure Identification-MI2C,
section 3 presents the phase-by-phase results of applying MI2C
within the scope of the XV Pan American and Parapan American Games and,
finally, section 4 presents the conclusions.
2
Methodology for Critical Infrastructure Identification MI2C
This methodology, one of
the set of methodologies presented in a previous issue of info@CITEL
[1], has been defined with eight phases (see Fig. 1):
·
Phase 1: Telecommunications services identification;
·
Phase 2: Definition of aspects for service evaluation;
·
Phase 3: Definition of aspect criticality levels;
·
Phase 4: Definition of the aspect weights;
·
Phase 5: Analysis of service criticality levels;
·
Phase 6: Mapping of critical telecommunications services;
·
Phase 7: Identification of telecommunications network
infrastructure;
·
Phase 8: Mapping of critical telecommunications infrastructure.

Fig. .
MI2C phases
3 Application
of MI2C within the scope of the Pan/Parapan 2007
MI2C was used to define the
critical portion of the telecom infrastructure in the scope of the XV
Pan American and the Parapan American Games (Pan/Parapan 2007) held in
Rio de Janeiro in July and August 2007.
3.1
Phase 1 Telecommunications services identification
Description: The main objective
here is to identify each and every telecommunications service,
considering the scope of the application.
Application: Anatel and the Organizing Committee of Pan/Parapan
2007 (CO-RIO) were invited to participate in multidisciplinary group
discussions to identify all of the relevant telecommunications
services (and the correspondent service providers) that could be used
during the events, either by athletes, coaches, event staff and
organizers (security, medical first-aid, cleaning, etc.),
representatives of local authorities (fire, ambulance and police
services), emergency rescue services spectators and the resident
population.
3.2
Phase 2 Definition of aspects for service evaluation
Description: The aspects that
will be used to evaluate the services identified in Phase 1 are based
on three distinct areas of interest: service users, society and the
State; some of them are quantitative while the others are qualitative.
Application: Meetings were held with Anatel, CO-RIO, researchers,
telecommunications specialists, information security specialists and
professors, amongst others, to identify the relevant aspects. Table 1
illustrates the results from this phase.
Table
1.
Relevant aspects to be analyzed for the Pan/Parapan 2007.

3.3
Phase 3 Definition of aspect criticality levels
Description: In this phase, the
level of criticality (qualitative and quantitative) for each aspect is
defined to allow the analyses of every service defined in Phase 1.
These levels of criticality should reflect the influence of the
telecommunications services for each aspect. There are several ways to
proceed with this definition, from a simple and generic classification
(using 3 levels: high, medium and low), to more complex
classifications (using n levels, where n is odd) if a
greater granularity is required.
Application: This analysis was performed during multidisciplinary
discussion group meetings with participants from Anatel, CO-RIO,
researchers, telecommunications specialists and, information security
specialists, amongst others. Three levels of criticality were defined:
High, Medium and Low (see Table 2).
Table 2.
Levels of criticality for the different aspects considered.

3.4
Phase 4 Definition of aspect weights
Description: In this phase the
different scenarios that can take place in a particular country are
mapped. Using aspects weighting it is possible to map not only the
real situation of the country, but also exercise hypothetical
scenarios as well; i.e. it is possible to establish different
scenarios by simply adjusting the aspects weighting.
Application: A group of specialists and analysts held meetings to
assign the aspects weightings. Since there are no extraordinary events
taking place in Brazil, the weights were set to 1 for all aspects,
except coverage, which was set to 0, as this factor is not relevant
at this moment and in this scope (see Table 3).
Table 3.
Definition of the weightings used to create scenarios.

3.5
Phase 5 Analysis of service criticality levels
Description: This phase is
responsible for analyzing the level of criticality for each
telecommunication service with respect to each aspect.
Application: This analysis was done by multidisciplinary
discussion groups in workshops. Some simple examples of questions that
were discussed are shown below:
·
Safety and health aspects: How does the telecommunication
service under analysis influence the health and safety aspect?
·
How critical is the service analyzed in the perspective of this
aspect?
·
Does this service contribute to, assist or facilitate this
aspect?
These simple questions were asked
for each telecommunication service identified in Phase 1. All the
services were analyzed from the perspective of each aspect (see Table
4). This is one of the most time consuming phases of the methodology.
Table
4.
Analysis of criticality.

3.6
Phase 6 Mapping of the critical telecommunications
services
Description: The main objective
of this phase is to convert the qualitative values to quantitative
ones in order to prioritize the telecommunication services. The method
of calculation employed can be a simple arithmetic average or
Analytical Hierarchy Process-AHP methodology, or other one method that
attains the desired objective.
Application: High, Medium and Low were mapped to the values 1, 2
and 3. Subsequently the calculation was performed and the ranking was
defined based on the average. The results are shown in Table 5.
Table
5.
Classification of level of criticality.

3.7
Phase 7 Identification of telecommunications network
infrastructure
Description: Identification of the telecommunications network
infrastructure used by critical services.
Application: Through workshops, meetings and questionnaires, and
with the support of the Brazilian telecom operators, the
telecommunications network infrastructure was identified. The
integration between different types of networks, such fixed and mobile
services, must be considered in this phase.
To
analyze the answers to the questionnaire, a semi-quantitative approach
was used, identifying information such as points that concentrate
traffic and functionalities, long distance strategic traffic routing
and infrastructure sharing. The 25 types of evaluation criteria were
grouped into 6 categories: Pan/Parapan 2007 sites, Infrastructure,
Transmission, Switching #1, Switching #2 and Switching #3. Table 6
illustrates the criteria for each category.
Table 6.
Criteria per category.

Adopting
this approach (categories vs. criteria) serves a twofold objective: a)
to minimize the presence of mistakes due to answer interpretation and
b) to minimize the number of criteria comparisons.
3.8
Phase 8 Mapping of critical telecommunications
infrastructure
Description: In this phase the
network infrastructure used by each and every critical service is
mapped in order to define the critical telecommunications
infrastructure. Performing this phase also requires an in-depth
knowledge of the telecommunications field and the relevant equipment
that supports the services. The required information was obtained
through workshops, questionnaires and study groups that included
telecommunications specialists and the people responsible for the
critical service that is being analyzed. In this phase the level of
granularity can be adjusted according to ones needs. The critical
network infrastructure found can be detailed at a high level (e.g.
building level) or a low-level (e.g. board level). Either way, all
critical services should always be included in the critical
infrastructure.
Application: The first step of is to attribute weights for each
category in the model formulated in the previous phase. Fig. 4 shows
the natural top-down approach for prioritizing the categories by
importance: the base of the pyramid (infrastructure) has the highest
weighting since, if it fails, all the categories above it will also
fail. The weights and normalization factors adopted for each category
are presented in Table 7. The normalization factor was introduced into
the model to eliminate the distortion caused by different categories
having different numbers of criteria.
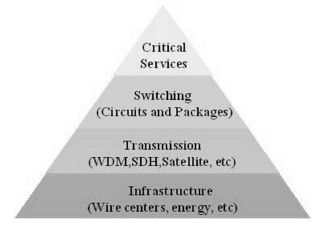
Fig.
.
Top-down approach to prioritize the categories.
Table
7.
Weights and normalization factor per category.

To obtain the final
scores, needed for the prioritization of the sites, the following
formula was used:

4
Results
Table 8 shows the 10 (ten) highest
ranked stations among all stations analyzed. This information allows a
more efficient resource allocation for infrastructure protection. For
security reasons, the real names of stations and operators have been
omitted.
Table 8.
Top ten stations ranked.

5
Conclusions
The
importance of critical telecommunication infrastructure identification
cannot be underestimated, since is the first step to an effective
infrastructure protection program. For this reason, it is important to
use a systematic approach like the one embodied in MI²C to
correctly identify the most critical parts of the telecommunication
infrastructure. This article has presented the application of the
Methodology for Critical Infrastructure Identification (MI2C),
for identifying the critical part of the telecommunication
infrastructure used during XV Pan American and Parapan American Games.
References
1.
Critical telecommunication infrastructure protection project,
info@CITEL, March 2007 issue.
Bibliography
1. Antón,
P.S.; Anderson, R.H.; Scheiern, M.; Mesic, R.M. Finding and Fixing
Vulnerabilities in Information Systems: The Vulnerability Assessment
and Mitigation Methodology. RANDs National Defense Research
Institute (2004).
2. Luiijf,
E.A.M., Burger, H.H.,Klaver, M.H.A.
Critical Infrastructure Protection in The Netherlands: A Quick-scan.
In: U.E. Gattiker (ed.), EICAR Conference Best Paper
Proceedings. Copenhagen, Denmark (2003).
3. Reinermann,
D.; Weber, J. Analysis of Critical Infrastructure: The ACIS
Methodology (Analysis of Critical Infrastructure Sectors). In:
Critical Infrastructure Protection (CIP) Workshop. Frankfurt, Germany
(2003).
4. Stonebumer,
G.; Goguen, A.; Feringa, A. Risk Management Guide for Information
Technology Systems. National Institute of Standards and Technology (NIST).
Special Publication 800-30 Rev A, Washington, USA (2004).
5. Dunn,
M.; Abele-Wigert, I. International CIIP Handbook 2006, Vol.
I: An Inventory of 20 National and 6 International Critical
Information Infrastructure Protection Policies. Center for
Security Studies. ETH Zurich (2006)
6. Dunn,
M.; Mauer, V.; Abele-Wigert, I. (eds.). International CIIP
Handbook 2006, Vol. II: Analyzing Issues, Challenges, and Prospects.
Center for Security Studies. ETH Zurich (2006).
7. Strogatz,
S.H. Exploring Complex Networks. In: Nature, 410 (2001)
8. Gorman,
S.P. Networks, Security and Complexity The role of public
policy in critical infrastructure protection. Edward Elgar
Publishing, Cheltenham, UK (2005).
9. Lewis,
T.G. Critical
infrastructure protection in homeland security: defending a networked
nation. John Wiley & Sons, New Jersey, USA
(2006).
João Henrique de Augustinis Franco, Fundação
CPqD
Regina Maria De Felice Souza, Agência Nacional de Telecomunicações
Sérgio Luís Ribeiro, Fundação CPqD
|
Notes:
[1] It is
important to note that MI2C, with the appropriate
changes, can be used to identity any other critical infrastructure
such as water, energy, transportation, health, etc.
[2]
Due to the strategic character of the project, sensitive
information was omitted or replaced.
|
|

